When you use Azure DevOps to deploy your projects you can connect it to Azure via different methods. The most convenient type of service connection is `Azure Resource Manager using service principal authentication`.
This type of connection creates application in your Azure Active Directory which is used as a Service Principal. Then for this application secret is generated, so Azure DevOps can connect to Azure. This secret token is expiring from time to time. The default time to live is 2 years but it may vary.
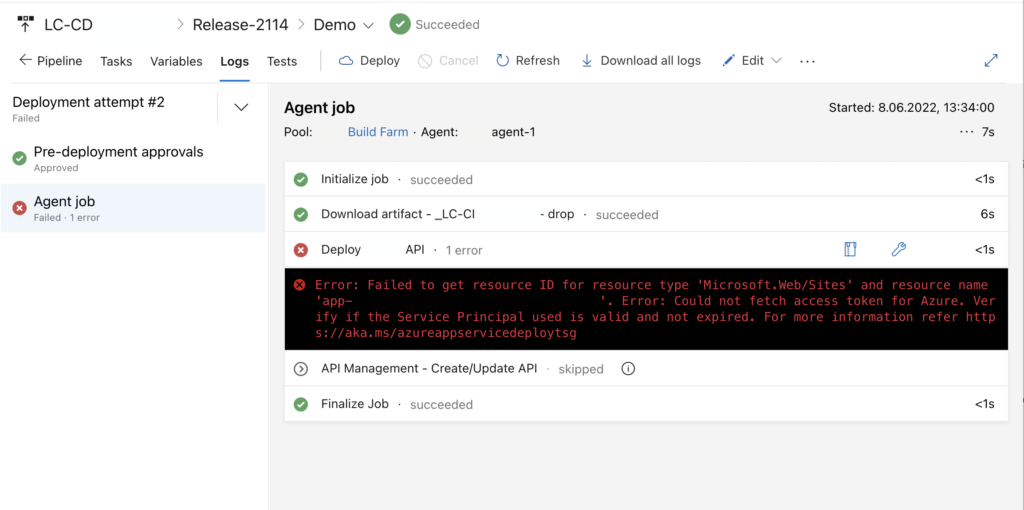
Once the secret is expired you will get this type of error when trying to deploy your code to Azure:
##[error]Error: Failed to get resource ID for resource type 'Microsoft.Web/Sites' and resource name 'XXX'. Error: Could not fetch access token for Azure. Verify if the Service Principal used is valid and not expired. For more information refer https://aka.ms/azureappservicedeploytsg
Verifying Service Connection (shorter)
This approach is shorter but I had some problems with it – wasn’t always working. Try with this one and if it doesn’t work try the longer one.
Microsoft Documentation describes the process as follows:
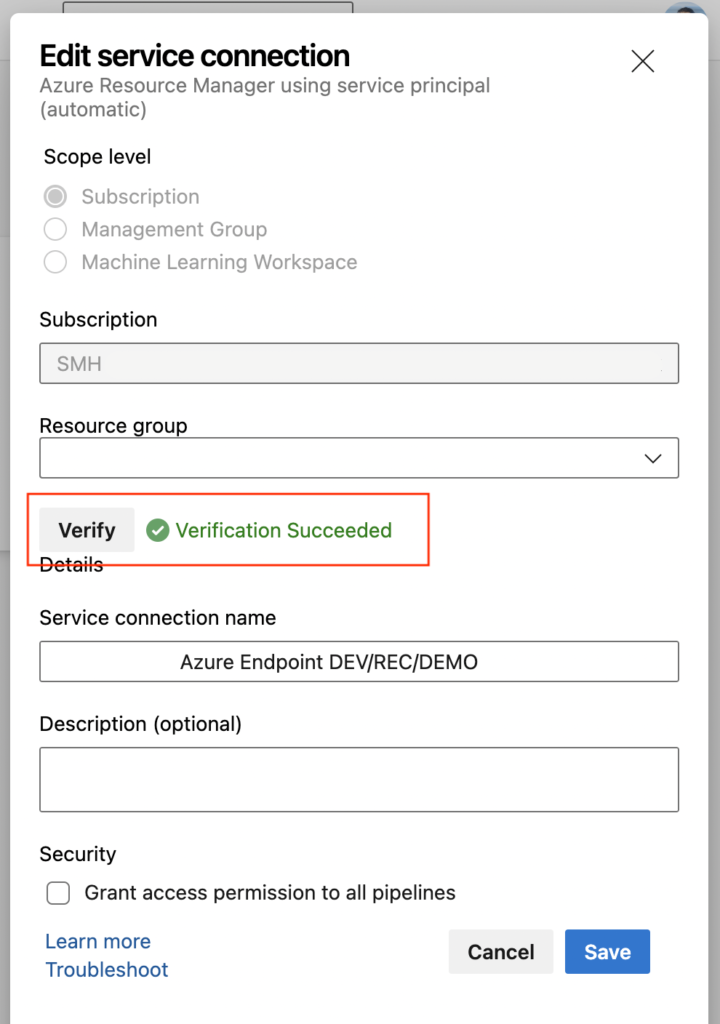
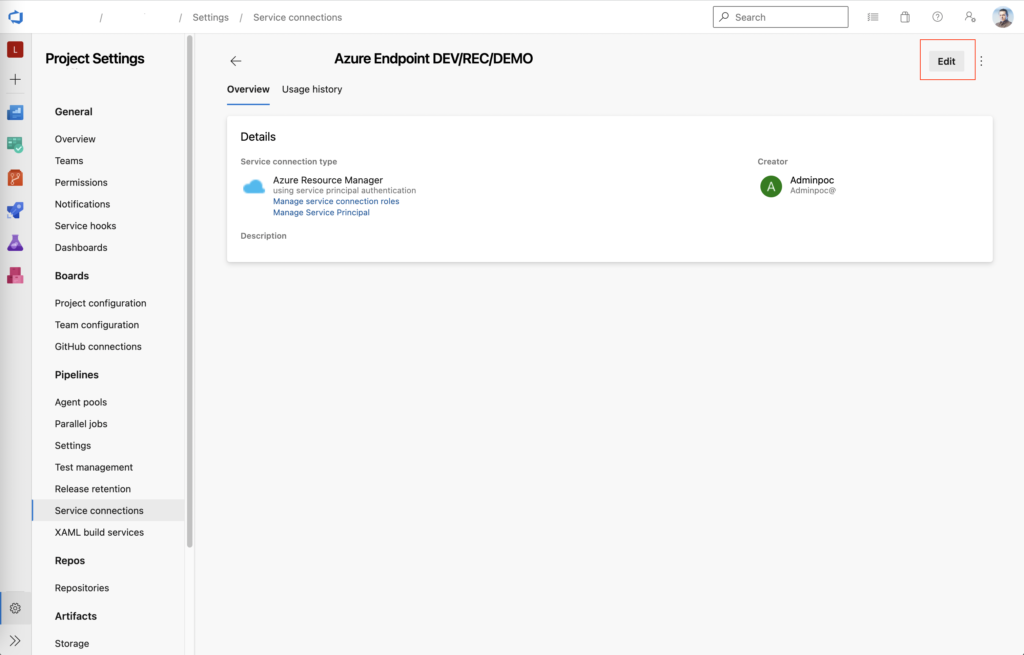
- Go to Project settings > Service connections, and then select the service connection you want to modify.
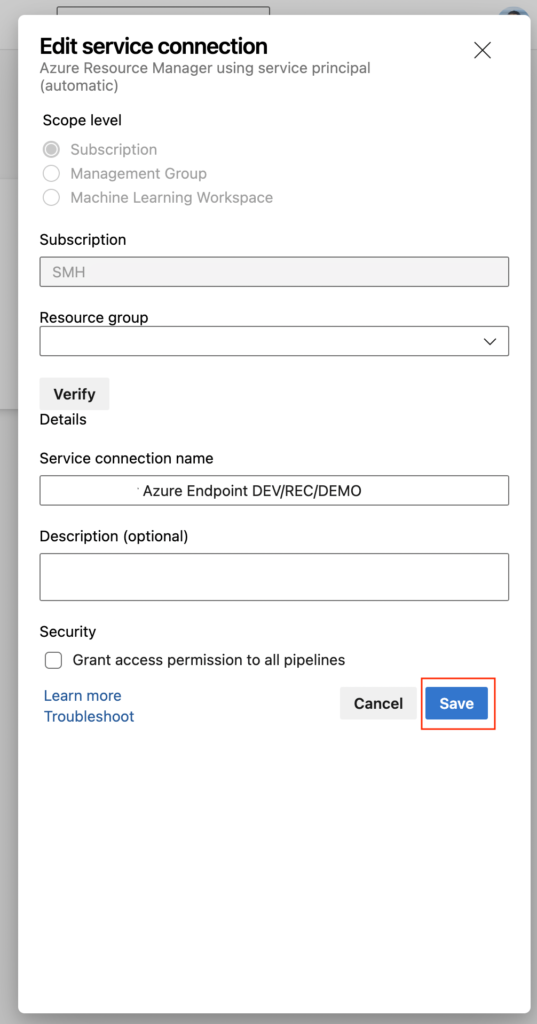
- Select Edit in the upper-right corner, and the select Verify.
- Select Save.
Removing secret and regenerating it (longer)
This approach is longer but was working for me without a problem. Use it if the first one doesn’t work.
So, how to renew the secret?
1. Make sure that you know what is the name of the Service Connection you’ll be renewing.
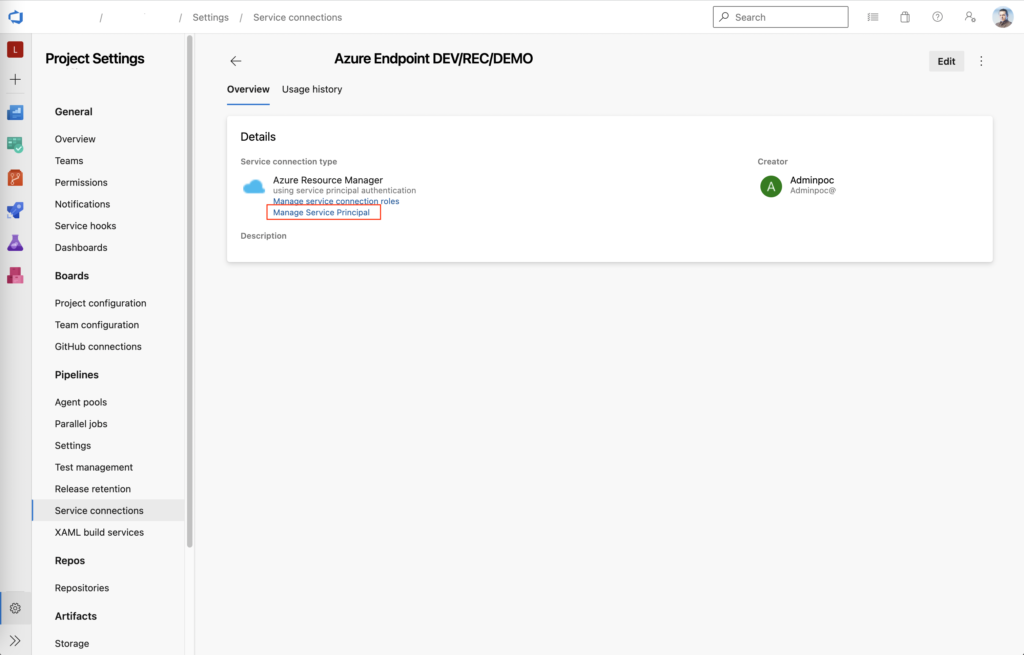
2. Go to Project Settings -> Service Connections (https://dev.azure.com/YOUR_ORG/YOUR_PROJECT/_settings/adminservices) and then to particular Service Connection you want to renew.
3. Then click on Manage Service Principal.
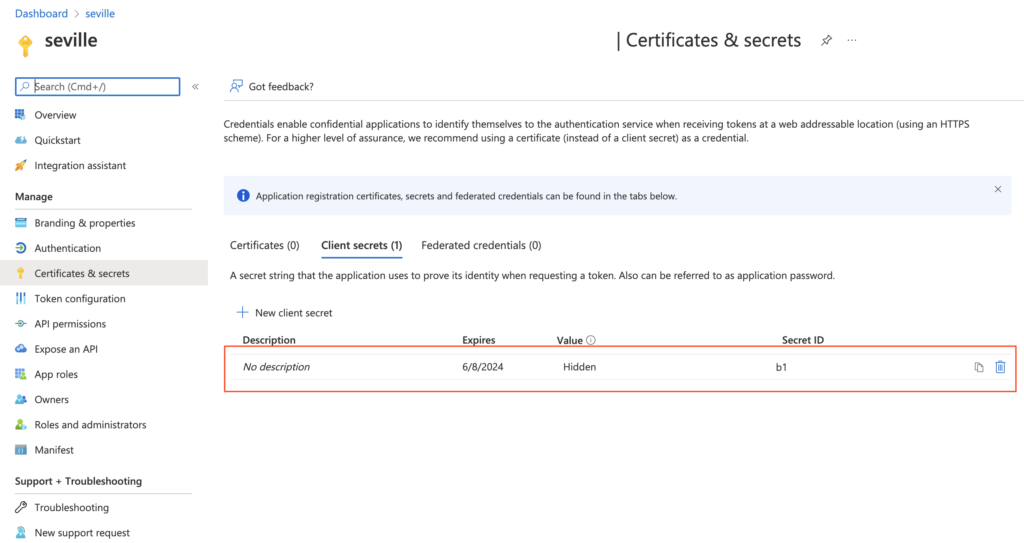
4. New tab with with Azure Active Directory application will be opened. Go to Certificates & secrets and remove expired secret.
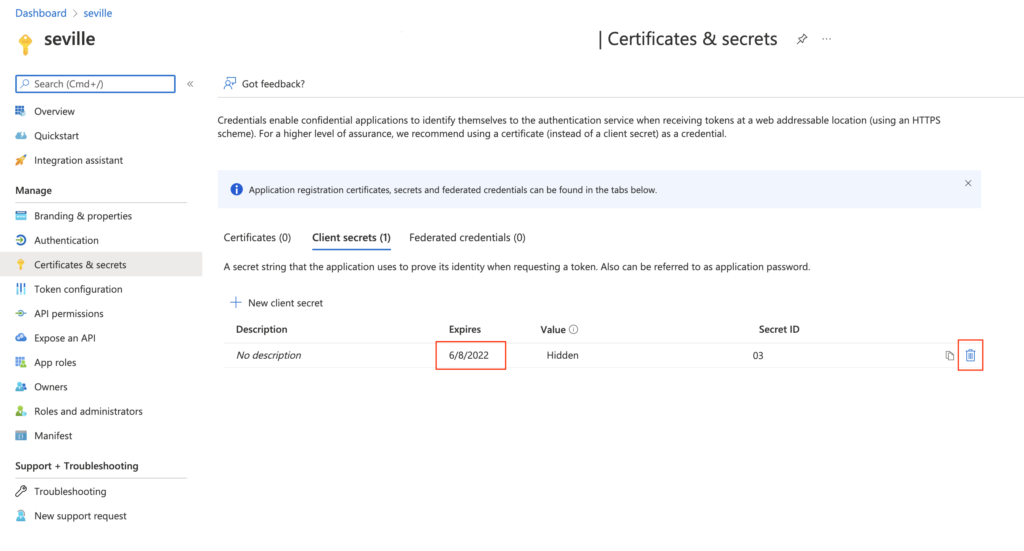
5. Go back to Azure DevOps Service Connection, click on Edit and then just Save. New secret should be generated in you Azure Active Directory!
This post is based on CamD answer from StackOverflow. Thank you!

